Ethereum now uses a Proof-of-Stake (PoS) consensus mechanism called Gasper. Gasper integrates two protocols: Casper the Friendly Finality Gadget (FFG), a protocol ensuring the finality of transactions; and a modified version of the Greedy Heaviest-Observed Sub-Tree (HLMD GHOST) for selecting the canonical chain.
In the unrealized justification reorg attack, the attacker manipulates the justified update of checkpoints to alter the “filtered/visible” view of the block tree for honest nodes. Specifically, the attacker creates and publishes a branch containing a new checkpoint, causing honest nodes to filter out the original branch (which is canonical according to weight) from their local fork-choice viable space, thereby achieving reorganization or blocking finality.
The unrealized justification reorg attack reveals a vulnerability in the interaction between Ethereum PoS’s GHOST layer and FFG layer:
The FFG layer is responsible for finality, but its justified state is directly used by the GHOST layer (as the starting point for fork choice);
The attacker can forge a “logically reasonable but not actually realized” justified checkpoint;
This causes the GHOST layer to discard the honest branch based on incorrect state;
Thus resulting in chain reorganization or even degraded security.
Attack Steps:
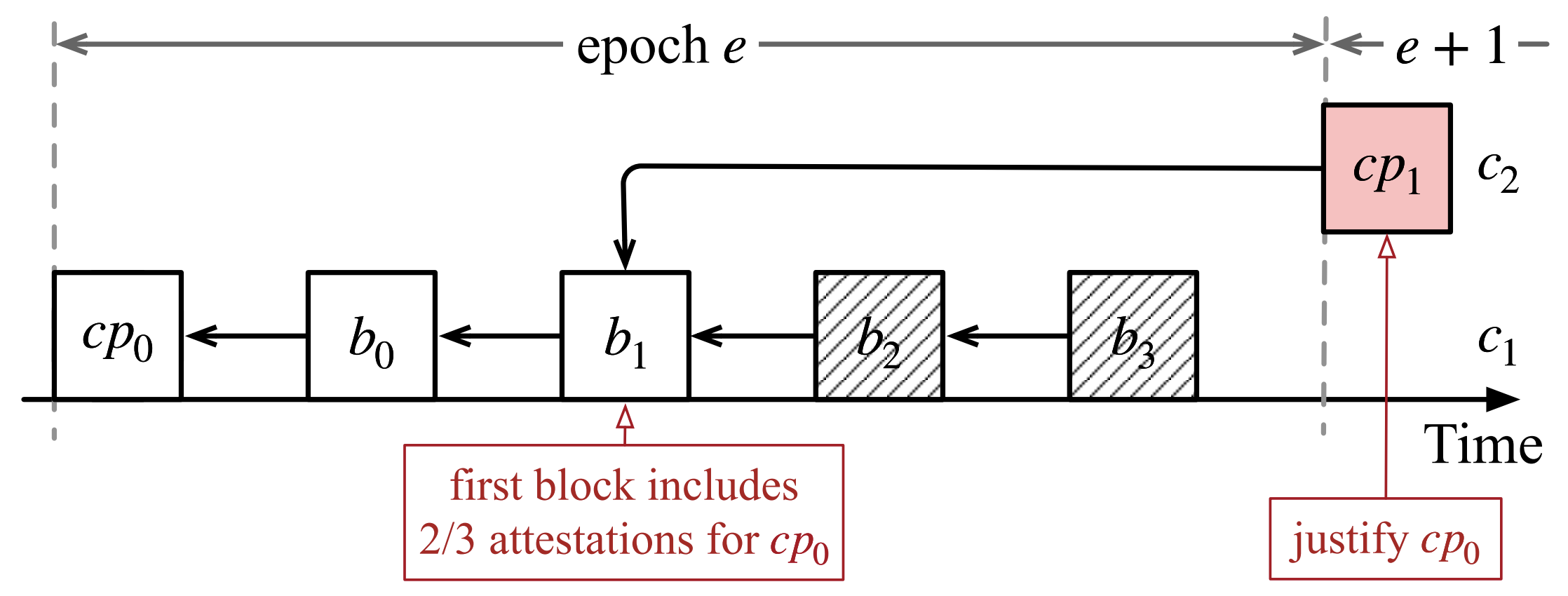
During normal operation in epoch
e, honest validators maintain the canonical chainc1with checkpointcp0, whereb1,b2, andb3are blocks in various slots within the epoch (b3is the last block of the epoch, andb1is an earlier block, specifically at slot 22).In epoch
e, blockb1(slot 22) happens to be the first block containing sufficient attestations to justifycp0(i.e., whenb1is seen, there are enough attestations pointing to it to makecp0justifiable), but in the honest global view, this justification is not immediately triggered on the canonical chain (or is not considered as last-justified by honest nodes).In epoch
e+1, the attacker (or a controlled proposer) constructs and publishes a checkpointcp1, deliberately setting its parent tob1(although the more reasonable parent on the honest chain should beb3). Thus,cp1belongs to an “early fork” chainc2(extending from the earlierb1), rather than the honestc1.When honest nodes receive this
cp1(along with its accompanying attestations/aggregates), according to pseudocode lines 22–23, they update the checkpoint state: locally treatingcp0as justified on chainc2(or pointingcp0’s last-justified to thec2view), thereby switching the last-justified root to the copy ofcp0underc2.Once
cp0becomes last-justified underc2, HLMD-GHOST’s FORKCHOICE (which selects the heaviest subtree starting from last-justified) will use the subtree undercp0inc2as the root to continue selecting the heaviest subtree. Therefore,c1(the honest chain) will be viewed as a “non-root path” and filtered out (i.e., FORKCHOICE no longer explores downc1), thus achieving de-selection/de-visibility of the honest chain.To ensure that
cp1can justifycp0, the attacker needsb1to appear at a position within the epoch such thatcp1can obtain sufficient attestations. In the diagram example:b1is chosen to be at slot ⌈32 × 2/3⌉ = 22.
Parameterized Calculation: Why Choose Slot 22? Why Orphan at Most 10 Blocks?
Key number: To mark a checkpoint cp0 as justified, ⌈32 × 2/3⌉ = 22 validator attestations are required (because checkpoints are based on epochs, each epoch has a fixed committee size, and the finality threshold is 2/3 of total weight; in terms of quantity, rounding up gives 22).
Attacker’s strategy: Let b1 appear at the 22nd slot of epoch e (counting from 1 to 32), so that after b1 is included/published, at most 32 − 22 = 10 subsequent slot blocks can still appear (these subsequent blocks are produced by honest proposers in the same epoch but after b1). Therefore, when the attacker publishes cp1 with b1 as parent in epoch e+1, at most these 10 subsequent honest blocks will be orphaned (no longer canonical). This design allows the attacker to keep the “damage” within an upper bound (compared to choosing a very early b1 which would orphan more blocks and be more easily detected).
Summary:
22 is because ⌈2/3 × 32⌉;
10 = 32 − 22 is the maximum number of honest blocks orphaned (within that epoch).
Attack Prerequisites and Cost
To successfully launch this type of unrealized-justification reorg, the attacker typically needs to satisfy:
Control a proposer for an epoch (specifically, the proposer who can propose
cp1in epoche+1), or be able to tamper with the proposer’s message to accept the attacker-provided parent.Replicate/obtain sufficient attestations or exploit network distribution, i.e., be able to make honest nodes see
cp1and accept its accompanying attestations (at least meeting the condition forcp0to be viewed as justified). This typically requires the attacker to control which messages are seen by which validators (targeted gossip), or release pre-aggregated attestations at the appropriate time.The attacker does not need to control 2/3 of the stake, but needs precise control over message propagation timing and parent specification.
The attacker bears certain risks: if honest nodes can detect selective/anomalous parent specification behavior in a short time, or if the protocol has additional checks on checkpoint updates (such as requiring aggregates or time windows), the attack will fail or the attacker will be slashed (if their behavior violates slashing conditions).
Attack cost: Resources related to attack success opportunity include proposer control (stake or time window), network layer control (partitioning or selective forwarding), and the risk of being discovered/punished.
Feasible Mitigation Measures
To resist unrealized-justification reorgs, it is recommended to place defenses on three parallel layers:
Propagation redundancy and aggregate verifiability (network + message format level) — Only switch
last_justifiedto that checkpoint when a verified aggregated attestation (≥2/3 signatures) is seen and the aggregate has been confirmed by other nodes through multiple independent propagation paths.Conservative in-place decision strategy (node level) — Nodes must meet the condition of “sufficient evidence and multi-path visibility” before locally updating
last-justified/ changing the fork-choice starting point; introduce “freshness / stability” checks for suspicious parents and reduce their weight.Detection/alerting/operational tools (monitoring layer) — Record parent pointers, attestation arrival timelines, automatically score and alert, and can trigger alternative propagation or replacement aggregators.